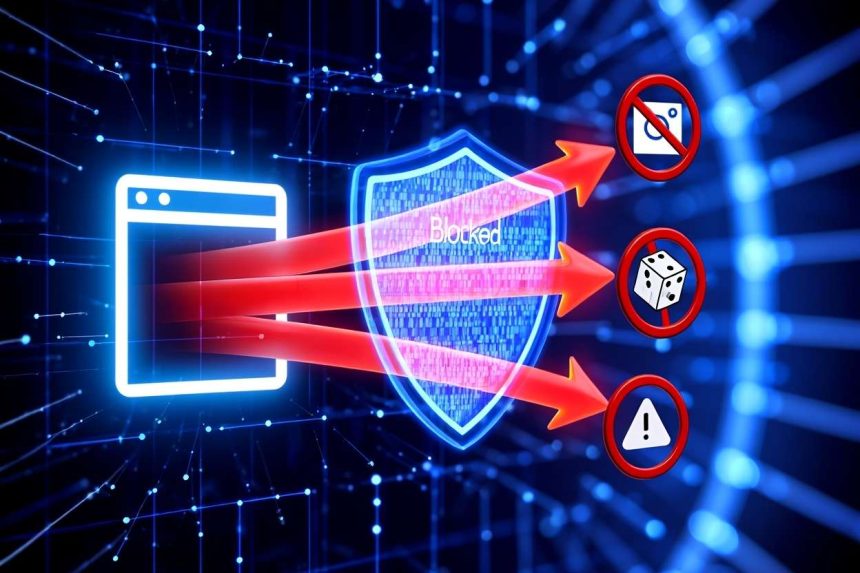
To use a firewall to block websites, create filtering rules that restrict access to specific domains or IP addresses. This method prevents users or devices from reaching unwanted online content across networks or individual devices.
Looking for a reliable way to control web access? Using a firewall to block websites is one of the most effective techniques in 2025 to protect devices, enforce policies, and maintain productivity. A firewall acts as a security gatekeeper, monitoring incoming and outgoing traffic, and with the right configuration, it can stop access to unwanted or risky sites.
As a cybersecurity professional with years of experience configuring firewalls for both home and enterprise networks, I’ve seen how properly applied website restrictions prevent malware infections, reduce distractions, and help organizations stay compliant. Parents can block social media to create focused study time, while IT administrators can filter high-risk domains to safeguard business data.
In this complete guide, you’ll learn not only the technical foundations behind firewall-based website blocking, but also step-by-step instructions for Windows, macOS, Linux, routers, and enterprise solutions. You’ll also see real-world use cases, troubleshooting tips, and best practices backed by trusted frameworks like NIST and recommendations from industry leaders.
In this guide, you’ll learn:
-
Why and when to use a firewall to block websites.
-
The technical foundations: domain vs IP filtering, SSL inspection.
-
Step-by-step tutorials for Windows Firewall, routers, and enterprise firewalls.
-
How to verify, troubleshoot, and prevent circumvention.
-
Complementary tools (DNS filtering, proxies, parental controls).
By the end, you’ll have the knowledge and confidence to configure website blocking responsibly—whether at home, school, or in a corporate environment.
Understanding the Purpose and Scenarios for Using a Firewall to Block Websites
Using a firewall to block websites is never a one-size-fits-all approach. Different groups apply website restrictions for different goals:
-
Parents: Enforce safe browsing habits and block harmful or distracting content.
-
Business administrators: Boost employee productivity and protect corporate networks from cyber threats.
-
Individuals: Limit personal distractions, control bandwidth, or prevent data leaks.
-
Educational institutions: Meet compliance requirements such as the Children’s Internet Protection Act (CIPA) and ensure a focused learning environment.
From my experience auditing both home and enterprise networks, the biggest difference lies in scope: device-level blocking applies rules on a single computer or phone, while network-wide blocking through routers or firewall appliances impacts every device connected. Another key factor is whether you block specific websites (e.g., facebook.com) or entire categories such as gambling or adult content, which requires more advanced filtering.
Finally, any use of a firewall to block websites should balance security benefits with privacy and ethical considerations. In workplaces and schools especially, transparency, user consent, and compliance with regulations like GDPR or CIPA are crucial to building both trust and effective protection.

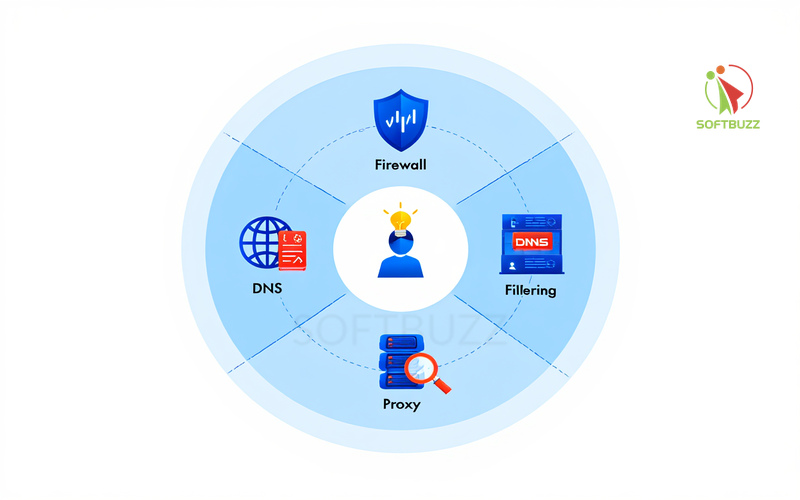
How Does a Firewall Block Websites? Core Concepts and Technical Foundations
At its core, using a firewall to block websites means applying security rules that decide which domains or IPs are allowed and which must be denied. Firewalls come in different forms, each suited to specific environments:
-
Software firewalls – installed on a single device, offering granular control per program.
-
Hardware firewalls – dedicated appliances that secure entire networks with advanced filtering.
-
Cloud-based firewalls – scalable solutions managed remotely, ideal for distributed teams.
-
Next-Generation Firewalls (NGFWs) – combine traditional blocking with intrusion prevention, application awareness, and SSL inspection.
Methods of Website Blocking
Firewalls typically rely on two main filtering methods:
-
Domain-based filtering: Blocks sites by domain name (e.g., facebook.com). This is user-friendly but less effective when sites use multiple domains or CDNs.
-
IP-based filtering: Restricts access to specific IP addresses. Strong against direct connections but limited when sites share or rotate IPs.
Challenges and Limitations
Even with rules in place, several challenges make blocking complex:
-
HTTPS/SSL encryption hides URLs unless advanced SSL inspection is used.
-
SNI (Server Name Indication) reveals domains for filtering, but newer protocols may encrypt it.
-
Dynamic IPs and CDNs make domain-to-IP mapping inconsistent.
-
Circumvention tools like VPNs, proxies, or encrypted DNS can bypass basic firewall rules.
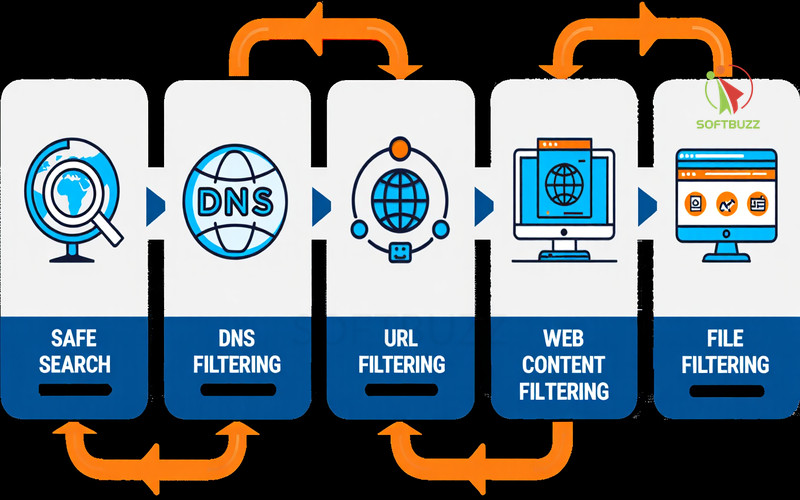
Complementary Solutions
To strengthen control, many admins combine firewalls with:
-
DNS filtering – blocking at the domain-resolution level.
-
Proxy servers or web gateways – inspecting and logging traffic before allowing it.
From experience auditing corporate networks, the most effective setups always combine multiple layers—firewalls, DNS filtering, and user awareness—rather than relying on a single method. Understanding these foundations helps individuals, parents, and IT teams apply website restrictions that are both effective and responsible.
Setting Up a Firewall to Block Websites: Step-by-Step Usage Guide
Using a firewall to block websites is one of the simplest yet most effective ways to control online access in 2025. Whether you’re a parent, IT admin, or casual user, the setup process depends on your platform and goals. From my experience helping both households and enterprises configure firewall rules, the key is choosing the right solution before creating custom filters.
Choosing the Right Platform
The right firewall depends on your setup—Windows and macOS for individuals, routers for families, and enterprise firewalls for business-scale control.
| Platform / Solution | Best Use Case |
|---|---|
| Windows Firewall / Defender | PCs in home or small offices |
| macOS Firewall | Mac user device-level blocking |
| Linux (iptables, ufw) | Granular server/desktop control |
| Router Firewalls (TP-Link, Netgear, Asus) | Network-wide blocking at home |
| Business Firewalls (FortiGate, Sophos, Cisco ASA) | Enterprise-grade filtering & compliance |
| Cloud Firewall Services | Remote or hybrid teams needing scalable control |
How to Block Websites Using Windows Firewall
On Windows, you can block a website by creating outbound rules that target its domain or IP address. If you’re new to this feature, see our guide on Windows Defender Firewall to understand how it works at the system level.
Steps:
-
Open Windows Defender Firewall with Advanced Security (search in Start menu).
-
Go to Outbound Rules → New Rule.
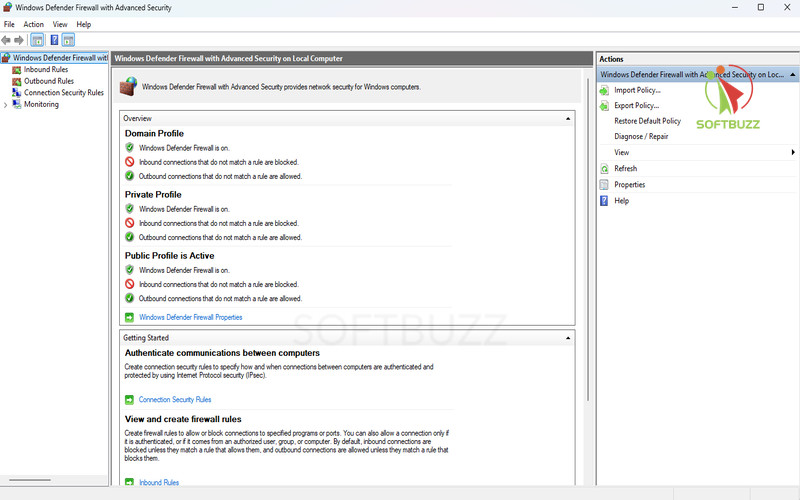
Windows Defender Firewall -
Select Program → browse to the app’s
.exe.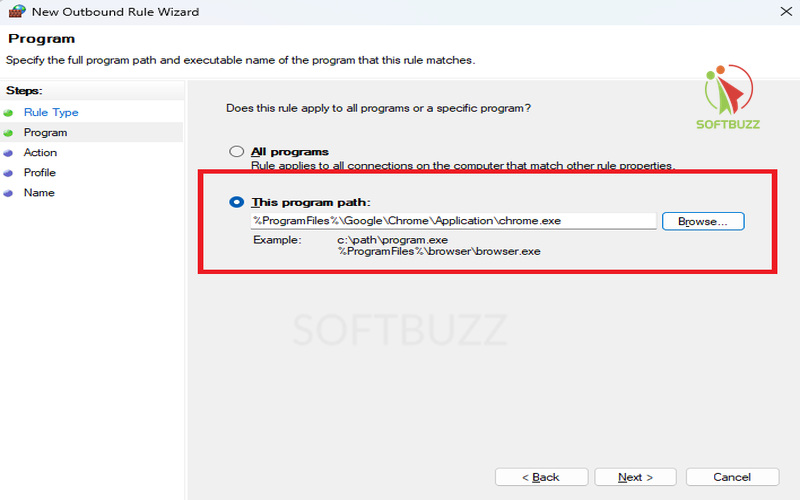
Select This program path -
Under Scope, add the website’s IPs (e.g., via
nslookup facebook.com). -
Choose Block the connection and apply to all profiles.
-
Name the rule (e.g., Block Facebook Outbound).
Test by opening the site. If blocked, you’ll see a connection error.
Note: Large sites like Facebook use multiple IPs/CDNs—combine firewall rules with DNS filtering for better results.
Blocking Websites on macOS, Linux, and Third-Party Firewalls
macOS and Linux require command-line rules, while third-party tools like Little Snitch or Comodo Firewall provide easier graphical controls.
-
macOS (Packet Filter – PF): Add blocking rules via Terminal, then reload config with
sudo pfctl -f /etc/pf.conf. -
Linux (iptables/ufw/firewalld): Example:
sudo iptables -A OUTPUT -d [IP_ADDRESS] -j DROP -
Third-party firewalls: ZoneAlarm, GlassWire, and Comodo provide advanced domain-based blocking and alerts.
Network/Router/Enterprise Firewall Blocking
Router and enterprise firewalls apply rules across all devices, making them ideal for parental control and corporate security.
-
Home routers (Netgear, TP-Link, Asus): Log into 192.168.1.1 → Access Control/URL Filtering → add domains to block.
-
Enterprise firewalls (FortiGate, Sophos, Cisco ASA): Provide deep packet inspection, user-based filtering, and compliance-ready reporting.
Advanced Methods: DNS Filtering, Proxy Use, and SSL Inspection
Combine firewalls with DNS filters, proxies, or SSL inspection for stronger, bypass-resistant website blocking.
-
DNS filtering: Services like OpenDNS or Quad9 block domains at the resolution stage.
-
Proxies & Web Gateways: Inspect and log all HTTP(S) traffic; enforce detailed rules.
-
SSL Inspection: Decrypts HTTPS for inspection, though requires careful management for privacy/legal compliance.
Pros & Cons:
-
DNS filtering = easy but bypassable with encrypted DNS.
-
Proxies = granular but add latency.
-
SSL inspection = accurate but complex to deploy.
Troubleshooting and Verifying Website Blocks
If your firewall fails to block a website, the issue usually lies in incomplete rules, encrypted traffic, or circumvention via VPNs. Proper testing and log reviews ensure your firewall to block websites works as intended.
Even the best firewall rules can fail if they’re not applied correctly or if users find ways around them. From my experience configuring enterprise firewalls, most issues stem from either missing IP ranges or overlooked encrypted traffic.
Common Reasons Why Website Blocks Fail
Most failures happen because of hidden domains, multiple IPs, or conflicting firewall rules. Identifying these gaps is the first step.
-
Websites using multiple IPs or CDNs not fully covered.
-
Encrypted SNI or DNS masking the domain name.
-
Users bypassing via VPNs, proxies, or Tor.
-
Firewall misconfigurations (scope errors, syntax mistakes, or low rule priority).
How to Troubleshoot Effectively
To verify your firewall to block websites is working, always check logs, test rules across devices, and validate rule priority.
-
Include all IP ranges related to the target domain.
-
Review firewall logs for blocked or allowed attempts.
-
Test rules on multiple devices and profiles.
-
Confirm block rules are active and prioritized above conflicting ones.
Preventing Circumvention
Stop users from bypassing your firewall by layering security with endpoint tools, monitoring, and regular audits.
-
Combine firewall rules with antivirus, parental controls, or endpoint monitoring.
-
Continuously track traffic and set alerts for suspicious activity.
-
Keep firewall definitions, DNS filters, and firmware updated.
-
Audit configurations regularly following NIST Cybersecurity Framework and CIS Controls.
Further Resources, Policies, and Ethical Considerations
Effective firewall use must balance security with privacy, compliance, and transparency.
For in-depth setup, see:
-
Microsoft Docs for Windows Defender Firewall.
-
Apple Developer Guides for macOS PF.
-
Vendor manuals (Sophos, Fortinet, Cisco).
-
Cloud DNS filtering providers such as OpenDNS or Quad9.
Organizations should also:
-
Implement Acceptable Use Policies (AUPs) explaining restrictions, enforcement, and user rights.
-
Ensure compliance with regulations like GDPR (privacy), CIPA (schools), and HIPAA (healthcare).
-
Be transparent with users about monitoring scope and purpose.
From my professional experience, the most sustainable approach to using a firewall to block websites is combining technical enforcement with clear policies—so users understand both the “how” and the “why.”
Quick Reference Appendix: Firewall to Block Websites Essentials
This appendix provides a fast, practical overview of the key terms and example commands you need when configuring a firewall to block websites in 2025.
Key Terms to Know
-
Firewall: A system enforcing network traffic rules to protect devices and networks from unauthorized access.
-
FQDN (Fully Qualified Domain Name): A complete domain name (e.g., www.example.com) used in domain-based filtering.
-
Proxy: An intermediate server that processes client requests, enabling filtering, logging, and access control.
-
DNS Filtering: Restricting website access by blocking domain name resolution requests at the DNS level.
Sample Rules for Blocking Websites
-
Windows Firewall (PowerShell example):
-
Linux (iptables example):
Best Practice Note
Use these sample rules as a baseline when configuring a firewall to block websites. Always adjust IP ranges or domains to match your specific network environment, and document changes for compliance. For enterprise setups, align configurations with frameworks like NIST or CIS Controls to ensure both security and audit readiness.
Frequently Asked Questions: Firewall to Block Websites
Here are the most common questions users ask when setting up a firewall to block websites in 2025, from HTTPS blocking to parental controls and compliance.
Q1: Can a firewall block HTTPS sites?
Yes, but only with advanced filtering.
A firewall can block HTTPS traffic by IP address or through SSL interception. This requires next-generation firewalls (NGFWs) or enterprise tools, as encrypted traffic hides domain details.
Q2: What’s the difference between a firewall and DNS filtering?
Firewalls filter traffic, DNS blocks at the name resolution stage.
Firewalls control access based on ports, IPs, and protocols, while DNS filtering stops domain lookups before a connection occurs. Combining both ensures stronger protection.
Q3: Which devices or networks benefit most from website blocking?
Schools, businesses, and homes with parental controls benefit the most.
Organizations use it to enforce security policies, while families apply it to create safe online environments.
Q4: Firewall vs. parental controls vs. browser extensions — which is best?
Firewalls offer stronger, network-wide protection.
Parental controls add user-level rules, and browser extensions are easy to set up but can be bypassed. For long-term reliability, firewalls remain the most effective.
Q5: How to schedule or time-limit website blocks?
Many firewalls support rule scheduling.
Some routers and firewalls let you set time-based restrictions. If not, scripts or third-party tools can automate scheduling.
Q6: How to block new or unknown domains?
Use category-based filtering with threat intelligence feeds.
Modern DNS services and NGFWs dynamically block harmful or uncategorized domains, staying ahead of emerging threats.
Conclusion
Using a firewall to block websites is one of the most effective ways in 2025 to secure devices, enforce policies, and boost productivity—whether at home, school, or in business environments.
By understanding the core technologies, choosing the right platform, and applying well-structured rules, you can implement website blocking with confidence. Complementary tools such as DNS filtering, proxies, and SSL inspection enhance protection, especially against encrypted traffic and circumvention attempts.
As a cybersecurity professional, I’ve seen organizations succeed when they treat firewalls as part of a layered defense strategy aligned with standards like NIST and CIS Controls. Regular audits, troubleshooting, and updates ensure that your firewall to block websites remains effective and compliant.
To recap:
-
Choose the firewall solution that matches your environment (Windows, macOS, Linux, routers, enterprise, or cloud).
-
Combine firewalls with DNS filtering, proxies, and monitoring for stronger coverage.
-
Balance restrictions with transparency and privacy to maintain ethical use.
For more step-by-step tutorials, explore our Windows category or return to the Softbuzz homepage for the latest security guides and practical tech tips.